Is your AI Vibe Coded
app leaking private data?
Scan your app and get a simple privacy and security report in seconds. No technical knowledge needed.
WORKS WITH
Scans apps built and deployed with
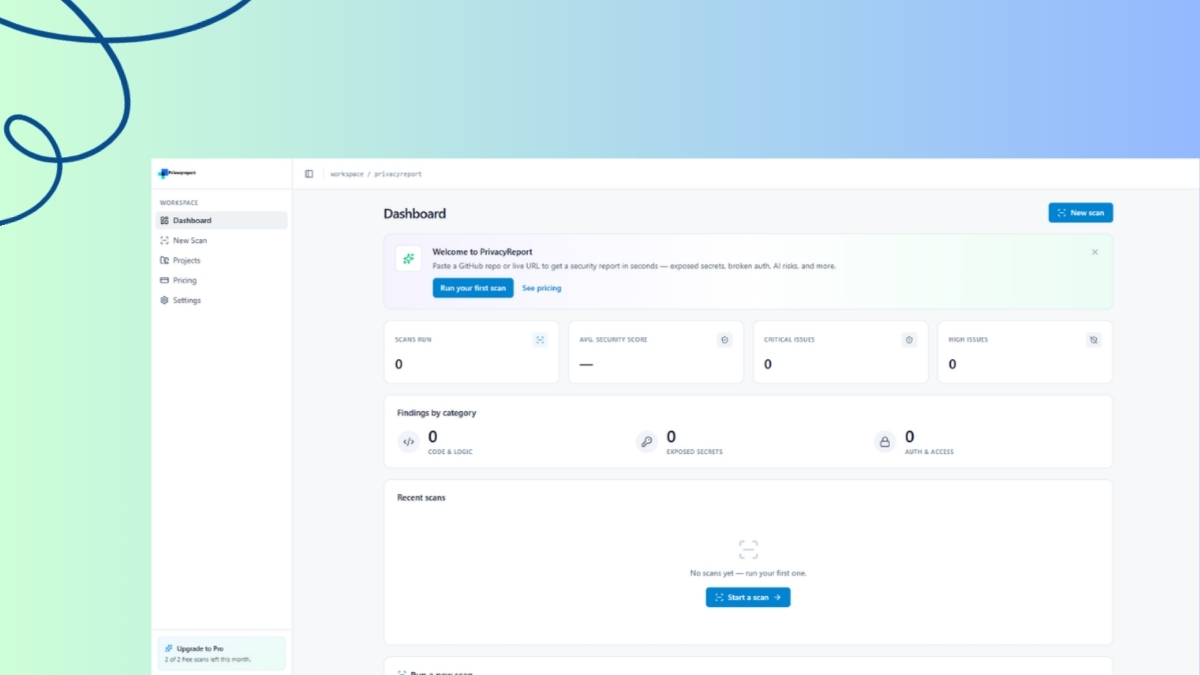
RESULT PREVIEW
Your report looks like this
Most AI-built apps are not safe. Vibe coding is fast, but security is slow. Get a plain-English card with your privacy score.
API keys exposed
Copilot and AI tools often paste secrets directly into your code. We flag them before they go public.
Hover to reveal →How we fix it
We scan your environment variables and hardcoded strings for known secret patterns (OpenAI, AWS, etc.) before deployment.
Protect SecretsOpen databases
Replit and Vercel deployments often ship with open databases accessible to anyone.
Hover to reveal →Instant Lockdown
We verify database connection strings and firewall rules to ensure your data stays private and unreachable from outside.
Secure DBData leaks
User emails, passwords, and private data silently flow out through misconfigured endpoints.
Hover to reveal →Leak Prevention
We analyze your API responses for PII (Personally Identifiable Information) and warn you before you leak user data.
Block LeaksHOW IT WORKS
Three steps. That's it.
We designed this for indie hackers and non-technical builders. No CLI, no complex configuration files. Just paste your link and let us do the heavy lifting.
-
1
Paste your app link
Drop in your GitHub repo URL or deployed app URL.
-
2
We scan for risks
Our scanner checks for exposed keys and 20+ other issues.
-
3
Get simple fixes
You get exact steps to fix each issue. No jargon.
GUIDED FIXES
We don’t just find problems — we fix them
Every issue comes with a clear, copy-paste solution tailored for the platform you are deploying on. You don't need to Google anything.
FEATURES
What we check
We scan for the most dangerous mistakes indie developers make.
- ✓ Exposed API keys
- ✓ Open endpoints
- ✓ AI prompt vulnerabilities
- ✓ Deployment misconfigurations
- ✓ User data exposure
- ✓ Comprehensive issue tracking
- ✓ Built-in remediation advice
- ✓ Secure by default configurations
How we stack up
| Feature |
|
Snyk
|
Semgrep
|
SonarQube
|
OWASP
|
Aikido
|
Checkmarx
|
Veracode
|
|---|---|---|---|---|---|---|---|---|
| Setup Process |
Just paste a URL. Done.
|
Requires devops setup
|
Requires devops setup
|
Needs a dedicated server
|
Needs a dedicated server
|
Requires devops setup
|
Enterprise onboarding
|
Enterprise onboarding
|
| Output & Reports |
Plain English. Easy to read.
|
Complicated jargon
|
Made for engineers
|
Huge PDFs
|
Made for engineers
|
Made for engineers
|
Huge PDFs
|
Huge PDFs
|
| Fixing Issues |
Gives you the exact code to fix it.
|
Points you to a wiki page
|
Shows rule violations
|
Tells you what broke
|
Tells you what broke
|
Gives general advice
|
Points you to a wiki page
|
Points you to a wiki page
|
| Pricing |
Free to start. Cheap to scale.
|
Enterprise only
|
Per user seat
|
Enterprise only
|
Free
|
Per user seat
|
Enterprise only
|
Enterprise only
|
PRICING
Plans for every builder
Start for free and upgrade as your app grows. No hidden fees.
Free
Try before you pay
- ✓ 1–2 scans per month
- ✓ Basic security score
- ✓ Limited issue detection
- ✕ No scan history
Pro
Everything you need to ship safely
- ✓ Unlimited scans
- ✓ Full issue detection
- ✓ AI-powered fix suggestions
- ✓ Full scan history
- ✓ Priority results
Builder
For teams shipping multiple apps
- ✓ Everything in Pro
- ✓ Multiple projects
- ✓ Continuous monitoring
- ✓ Email & Slack alerts
- ✓ API access
Don’t launch an unsafe app
Ensure your app is secure before you share it with the world.
Scan My App Now — Free