The numbers are stark: In 2026, over 31% of global internet users utilize VPNs, but while a significant portion seeks legitimate privacy, an estimated $15.4 billion in global ad spend is siphoned annually by sophisticated click-fraud bots hiding behind encrypted tunnels. For the modern CMO, best practices for implementing vpn detection in marketing are no longer just a security checkbox; they are a fundamental requirement for protecting marketing ROI and ensuring data veracity in an increasingly opaque digital landscape.
1. The Strategic Necessity of Network Transparency
In an era where digital footprints are increasingly obscured, marketers face a paradox: respecting user privacy while maintaining the integrity of their data. Without robust detection, your analytics become “poisoned,” leading to wasted spend on bot traffic and inaccurate geographical targeting. According to Deloitte’s 2026 Tech Trends, organizations that move beyond “experimental AI” to “operational security” gain a definitive competitive advantage.
2. What Is VPN Detection in 2026?
Modern VPN detection is the technical process of identifying whether an incoming web request originates from a virtual private network, proxy, or Tor exit node. Unlike the “binary blocking” of the past, VPN detection as a strategic asset now uses advanced fingerprinting to categorize traffic into risk tiers. This ensures that users seeking a secure connection to 123Movies alternatives or other high-risk sites do not compromise your platform’s internal security.
3. The 3 Pillars of Marketing Integrity
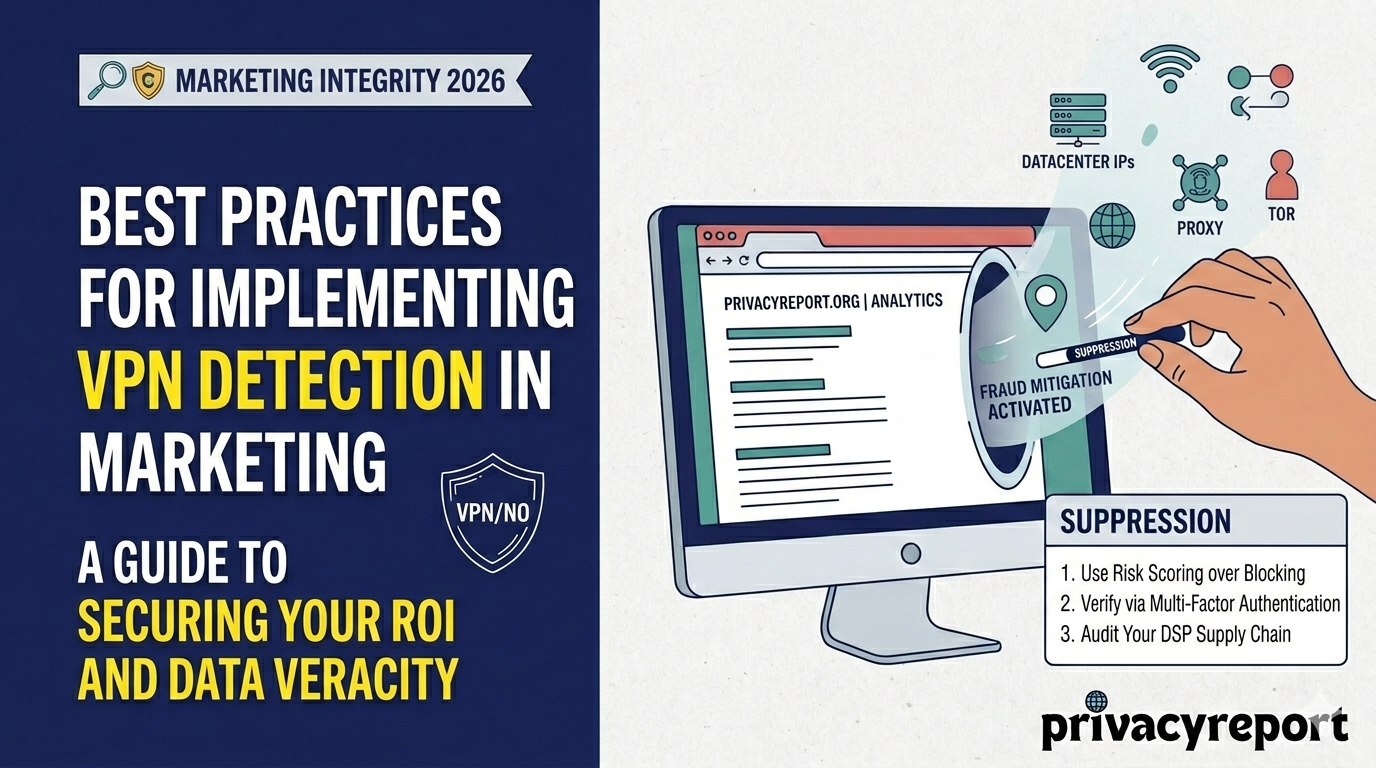
To maintain a competitive advantage, organizations must build their best practices for implementing vpn detection in marketing on three foundational pillars:
- Pillar 1: Data Veracity: Ensuring geographical analytics are not “poisoned” by spoofed locations.
- Pillar 2: Fraud Mitigation: Identifying botnets that use rotating residential VPNs to mimic human behavior.
- Pillar 3: Compliance Precision: Aligning with Gartner’s 2026 Market Guide on Managed Security Services to ensure network visibility remains high without violating user trust.
4. Ad Fraud vs. Legitimate Privacy: The Contextual Gap
Understanding the difference between a privacy-conscious user and a malicious bot is critical for ROI.
| Context A: Legitimate Privacy | Context B: Ad Fraud / Malicious |
| User: Remote worker at a café. | User: Headless browser script. |
| Network: Known commercial VPN. | Network: Obscure “bulletproof” proxy. |
| Behavior: High session duration. | Behavior: 0.2s page dwell time. |
| Goal: Data encryption. | Goal: Bonus abuse or click-revenue theft. |
6. Best Practices for Implementation
Implementing detection requires a surgical approach. Organizations should follow the NIST 800-63-4 Guidelines for digital identity to balance security with frictionless marketing.
- Risk Scoring over Blocking: Assign a risk score to every IP.
- Verify via MFA: Trigger multi-factor authentication for suspicious origins.
- Audit Your Supply Chain: Ensure your DSPs (Demand Side Platforms) utilize real-time detection logic.
- Monitor “Residentials”: Pay close attention to residential proxies, which are often used for sophisticated “human-like” fraud.
7. Regulatory Compliance: GDPR & FTC Truth-in-Advertising
In 2026, the FTC’s Truth-in-Advertising standards apply to the technology layer. If your marketing reports claim “1 million unique US visitors,” but 200,000 are bot-traffic from VPNs, you risk regulatory scrutiny. Furthermore, under GDPR Article 6, using VPN detection for “fraud prevention” is considered a Legitimate Interest, making it a legal necessity for European market engagement.
15. Frequently Asked Questions
Q1: Will VPN detection hurt my SEO?
Ans: No. Search engine crawlers (like Googlebot) do not use VPNs. Proper detection ensures your site remains visible to engines while invisible to fraudsters.
Q2: Is VPN detection legal under GDPR?
Ans: Yes, provided it is used for “fraud prevention,” which is considered a Legitimate Interest under the current legal framework.
Q3: Can’t fraudsters just use residential IPs?
Ans: They try, but modern detection uses behavioral biometrics and TCP/IP fingerprinting to identify the “clues” left behind by proxy servers, even on residential connections.
Q4: How does this impact my Google Ads budget?
Ans: By excluding known datacenter ranges, you can reduce wasted spend by up to 25% ensuring your ad budget reaches real humans rather than automated scripts.
Conclusion
The emergence of sophisticated “shadow traffic” in 2026 requires a shift in how we view network security. Implementing best practices for implementing vpn detection in marketing is no longer optional—it is the difference between a high-performing, data-driven campaign and one that is slowly drained by invisible actors. Protect your integrity, secure your ROI, and ensure your brand remains a leader in the digital sovereignty era.
Leave a Reply