Introduction: The Masked Traffic Problem Is Getting Worse
Here is a number worth sitting with.
As of 2025, an estimated 31% of internet users globally use a VPN at least once a month. In some markets — the Middle East, Southeast Asia, parts of Latin America — that number climbs significantly higher. And that is just consumer VPN usage. Add corporate VPN traffic, proxy servers, Tor exit nodes, residential proxies, and datacenter IP ranges being used for anonymous browsing, and the actual proportion of masked internet traffic is substantially larger.
For most businesses operating online, this creates a quiet but growing problem.
Your analytics are showing traffic from London when the users are actually in Lagos. Your geo-targeted ad campaigns are serving content to entirely the wrong audiences. Your fraud prevention system is missing account takeover attempts because the attacker is routing through a residential proxy that looks like a legitimate home user. Your regional pricing strategy is being exploited by customers connecting through VPN servers in lower-price markets.
None of this is hypothetical. It is happening right now, across millions of websites and applications, and most businesses have no systematic way of addressing it.
VPN detection APIs exist specifically to solve this problem. They analyze incoming IP addresses and return intelligence about whether that IP belongs to a VPN service, proxy server, Tor exit node, datacenter, or other anonymizing infrastructure — giving businesses the information they need to make smarter decisions about how to handle masked traffic.
The market for these APIs has matured significantly. There are now dozens of providers offering VPN detection capabilities, ranging from basic IP blacklist lookups to sophisticated multi-signal intelligence platforms that combine IP analysis with behavioral signals, network topology data, and machine learning models trained on billions of data points.
This article covers the best VPN detection APIs available in 2025, what distinguishes the strongest from the weakest, and what businesses should look for when choosing a solution for their specific use case.
What Makes a VPN Detection API Actually Good?
Before getting into specific providers, it is worth establishing what separates a genuinely useful VPN detection API from a mediocre one. Because in this market the quality difference between providers is enormous and the consequences of choosing poorly — high false positive rates, missed detections, stale data — are significant.
Database freshness and coverage — VPN infrastructure changes constantly. New servers come online, IP ranges rotate, providers launch and shut down. A detection database that is not updated continuously will miss recent VPN infrastructure and flag IPs that have been reassigned from VPN use to legitimate residential or commercial use. The best providers update their databases in near real time rather than weekly or monthly batches.
Detection breadth — VPN is just one category of masked traffic. A strong detection API distinguishes between VPNs, datacenter proxies, residential proxies, Tor exit nodes, open proxies, and hosting provider IPs — because each category represents a different risk profile and warrants a different business response.
Residential proxy detection — This is where most VPN detection APIs fall short. Residential proxies route traffic through real consumer IP addresses, making them extremely difficult to distinguish from legitimate home users through IP analysis alone. The best APIs incorporate signals beyond IP reputation to catch residential proxy traffic.
False positive rates — A VPN detection API that incorrectly flags legitimate users as VPN users is actively harmful to your business. Every false positive is a real customer being incorrectly treated, a legitimate transaction being blocked, or an analytics data point being incorrectly discarded. Providers that optimize purely for detection rate at the expense of precision create as many problems as they solve.
Response speed — VPN detection typically happens in the critical path of a user request — at login, at checkout, on page load. API response times measured in hundreds of milliseconds create user experience problems. The best providers return results in single-digit milliseconds through globally distributed infrastructure.
Confidence scoring — Binary yes/no VPN detection is less useful than a nuanced confidence score that lets businesses apply different responses to high-confidence detections versus ambiguous cases. Providers that return rich metadata alongside their detection decision give businesses far more flexibility.
The Best VPN Detection APIs for Masked IP Traffic in 2025
1. IPQualityScore
IPQualityScore has established itself as arguably the most comprehensive IP intelligence platform in the VPN detection space, and its reputation among fraud prevention professionals is strong enough that it is frequently the first recommendation when businesses ask where to start.
The core of IPQualityScore’s VPN detection capability is its Proxy Detection API, which analyzes incoming IP addresses across an unusually broad range of signals. Beyond standard IP reputation database lookups, the platform incorporates active probing of suspicious IP ranges, machine learning models trained on fraud pattern data from across its customer network, and behavioral signals that help identify residential proxies that would defeat IP-only analysis.
What makes IPQualityScore particularly strong for businesses dealing with sophisticated masked traffic is its layered risk scoring system. Rather than returning a simple VPN flag, the API returns a fraud score from zero to one hundred alongside specific flags for VPN, proxy, Tor, bot, and recent abuse activity. This granularity lets businesses implement nuanced responses — stepping up verification for medium-risk scores, blocking only the highest-risk traffic, and passing low-risk traffic without friction.
The platform covers the full spectrum of masked traffic categories that matter in 2025 — commercial VPNs, datacenter proxies, residential proxies, mobile proxies, Tor exit nodes, and compromised devices being used as unwitting proxies in botnet infrastructure. This breadth is important because sophisticated fraudsters have largely moved away from easy-to-detect datacenter VPNs toward residential and mobile proxies that most simpler detection services miss entirely.
IPQualityScore’s API response times are consistently fast — typically under fifty milliseconds globally — making it viable for real-time use in authentication flows, checkout processes, and ad serving decisions without meaningfully impacting user experience.
For businesses dealing specifically with ad fraud, the platform’s click fraud detection capabilities that sit on top of its VPN detection foundation provide additional value — identifying not just masked traffic but masked traffic exhibiting the behavioral patterns of click fraud rather than genuine user intent.
Pricing is consumption-based with a generous free tier suitable for development and low-volume production use, scaling to enterprise pricing for high-volume applications.
2. IPinfo
IPinfo has built one of the most trusted and developer-friendly IP intelligence platforms available, with a VPN detection product that reflects the same commitment to data quality and usability that has made its broader IP data products popular among engineers at companies of all sizes.
The IPinfo Privacy Detection API identifies VPN usage, proxy servers, Tor exit nodes, relay services like Apple Private Relay and iCloud Private Relay, and hosting provider IPs that are being used for anonymization rather than legitimate server hosting. The distinction between these categories is important and something that simpler detection services often collapse into a single flag.
Apple’s iCloud Private Relay and similar relay services from major technology companies represent a genuinely new category of masked traffic that older VPN detection approaches handle poorly. These services route traffic through Apple and Cloudflare infrastructure in ways that preserve user privacy while still looking like legitimate traffic from a well-known technology company. IPinfo has invested specifically in identifying and flagging this category of relay traffic — important for businesses that need to know their traffic is relay-masked even when it is not coming from a traditional VPN service.
IPinfo’s data quality reputation is built on its approach to IP geolocation accuracy — one of the best in the industry — which translates directly into VPN detection quality because geolocation discrepancy is one of the signals used to identify masked traffic. When an IP’s claimed location does not match its network routing patterns, that discrepancy is evidence of anonymization that IPinfo’s models are well-positioned to catch.
The API is straightforward to integrate, with clear documentation, SDKs for every major programming language, and response formats that are consistent and predictable. For development teams that have struggled with poorly documented IP intelligence APIs — and there are many in this space — IPinfo’s developer experience is a genuine differentiator.
Response times are fast across IPinfo’s globally distributed infrastructure, and the platform’s uptime track record is strong — important for businesses integrating VPN detection into availability-critical paths like user authentication.
3. MaxMind minFraud and GeoIP2
MaxMind is one of the oldest and most respected names in IP intelligence, with a track record in geolocation and fraud detection that predates most of its current competitors by a decade or more. Its minFraud platform and GeoIP2 data products remain widely deployed across the internet and continue to evolve meaningfully.
MaxMind’s approach to VPN detection is notable for its integration of IP intelligence with broader transaction risk scoring. The minFraud API does not just tell you whether an IP is a VPN — it tells you the risk score for an entire transaction taking into account the IP characteristics, the device fingerprint, the email address, the shipping address, and dozens of other signals simultaneously. For e-commerce and financial services businesses where VPN detection is one input into a broader fraud decision, this integrated approach is significantly more useful than a standalone IP check.
The GeoIP2 Insights product provides granular IP intelligence that includes connection type — identifying corporate networks, consumer broadband, mobile networks, hosting providers, and anonymizing VPNs — alongside the geolocation data that MaxMind has long been known for. The combination of accurate geolocation and connection type classification provides context that helps businesses distinguish between a legitimate corporate VPN user working remotely and a fraudster routing through an anonymizing service.
MaxMind’s database update frequency has historically been a criticism — weekly updates are less responsive to new VPN infrastructure than the real-time or daily updates offered by some competitors. The company has been working to address this but it remains a consideration for businesses dealing with sophisticated actors who specifically use fresh VPN infrastructure to avoid detection.
For businesses already using MaxMind geolocation data, adding VPN detection through the same API relationship is a natural and low-friction expansion. For businesses starting fresh, MaxMind’s track record and the breadth of its data — including its extensive database of IP addresses associated with fraudulent activity accumulated over years of transaction monitoring — make it a strong contender.
4. Cloudflare Radar and Cloudflare’s IP Intelligence
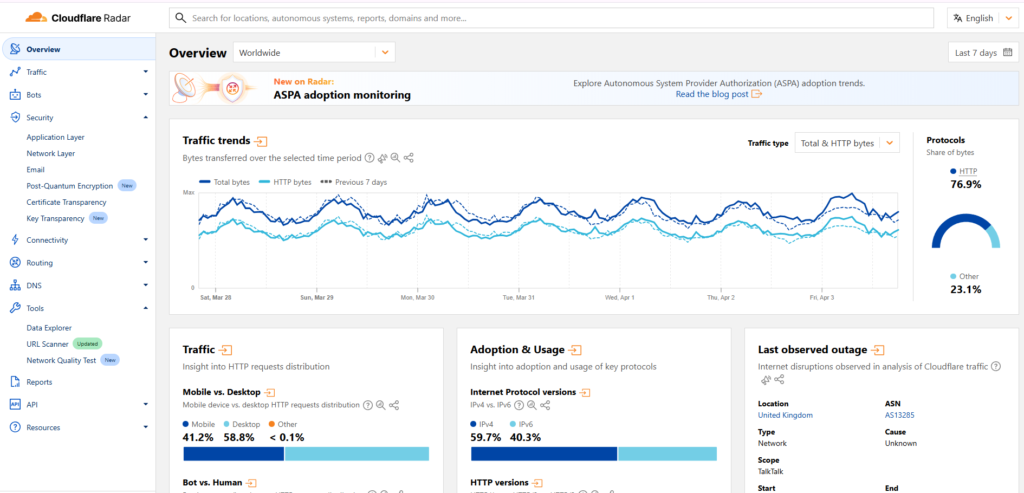
Cloudflare occupies a unique position in the internet infrastructure landscape that gives its IP intelligence products a data advantage that no traditional IP intelligence vendor can replicate. Cloudflare sits between a significant fraction of the world’s internet traffic and the servers that serve it — giving it visibility into traffic patterns, IP behavior, and network activity at a scale that is genuinely unmatched.
Cloudflare’s IP Intelligence API, part of its broader security product portfolio, draws on this unique network visibility to provide VPN and proxy detection that reflects actual observed traffic behavior rather than just database lookups against known VPN IP ranges. When Cloudflare’s network has observed an IP address behaving in ways consistent with VPN or proxy use — rotating through multiple apparent users, exhibiting traffic patterns inconsistent with a single residential connection, appearing in known anonymizing infrastructure — that behavioral evidence informs its IP intelligence products in near real time.
For businesses already using Cloudflare for CDN or security services, the integration of Cloudflare’s IP intelligence into their applications is straightforward and carries cost efficiencies. For businesses not already in the Cloudflare ecosystem, the API is available as a standalone product though the commercial terms and access model differ from pure-play IP intelligence vendors.
Cloudflare’s position also gives it strong visibility into the relay services and privacy proxies operated by major technology companies — Apple Private Relay, iCloud Private Relay, and similar services that route through Cloudflare infrastructure — making it particularly well-positioned to identify this increasingly common category of masked traffic.
5. IPAPI and Abstract API
For businesses with simpler VPN detection needs — particularly smaller applications, early-stage products, or use cases where detection depth is less critical than ease of integration and cost — IPAPI and Abstract API represent the accessible end of the VPN detection market without being meaningfully inferior on the basics.
IPAPI’s VPN detection layer sits on top of its core IP geolocation API, returning a security object alongside location data that flags VPN, proxy, Tor, and hosting provider IPs. The integration is about as simple as IP intelligence APIs get — a single endpoint call returns everything a developer needs to make basic masked traffic decisions.
Abstract API takes a similar approach, with clean documentation, generous free tiers, and detection coverage that handles the most common VPN services and datacenter proxy ranges reliably. For applications where the threat model is primarily opportunistic VPN use by regular consumers rather than sophisticated residential proxy networks used by organized fraudsters, Abstract API’s detection capabilities are sufficient and its developer experience is genuinely pleasant.
Neither platform matches the detection depth of IPQualityScore or the data quality reputation of MaxMind for sophisticated masked traffic scenarios. But for the large category of applications where good-enough detection implemented quickly and cheaply is more valuable than best-in-class detection implemented after weeks of evaluation and integration work, they deserve serious consideration.
6. Scamalytics
Scamalytics brings a fraud-first perspective to IP intelligence that makes it particularly valuable for businesses where VPN detection is primarily motivated by fraud prevention rather than analytics accuracy or geo-targeting integrity.
The platform has built its IP reputation database through direct operation of honeypot networks and fraud intelligence partnerships — giving it visibility into IP addresses associated with active fraud campaigns that purely database-driven approaches may not have. When a VPN server or proxy IP has been used in fraudulent transactions, phishing campaigns, or account takeover attempts observed through Scamalytics’s own intelligence infrastructure, that history is reflected in its risk scoring in ways that newer or less operationally active providers cannot match.
The Scamalytics API returns a fraud score alongside specific flags for proxy, VPN, Tor, and web hosting IPs, with the fraud score reflecting not just the IP type but the historical abuse record associated with that IP. For businesses in e-commerce, financial services, or any industry where IP-based fraud is a significant operational problem, this abuse history dimension adds meaningful signal.
Scamalytics also maintains a free tier suitable for low-volume applications and development testing, with clear and predictable scaling to commercial tiers as volume grows.
7. Spur
Spur is a specialized IP intelligence provider that has built its reputation specifically on residential proxy and anonymization infrastructure detection — the hardest part of the masked traffic problem and the area where most general-purpose IP intelligence APIs fall shortest.
The challenge with residential proxies is that the underlying IP addresses are genuinely residential — assigned to real home internet connections — making them invisible to detection approaches that rely on identifying known VPN or datacenter IP ranges. Spur’s approach focuses specifically on identifying the behavioral and network characteristics of IP addresses being used as residential proxy nodes, regardless of whether those IPs appear on any known VPN or proxy list.
Spur maintains what it describes as the most comprehensive database of residential proxy infrastructure in existence, built through a combination of active network research, honeypot deployment, and analysis of anonymization network topology. For businesses dealing with sophisticated fraud actors who have specifically moved to residential proxies to defeat conventional VPN detection, Spur’s specialized focus addresses a gap that broader IP intelligence platforms leave open.
The API is more technical in its integration requirements and documentation than some of the more developer-friendly options on this list, reflecting its positioning toward security professionals and fraud teams rather than general developers. But for businesses where residential proxy detection is a genuine operational priority, Spur’s specialized depth is worth the additional integration investment.
Choosing the Right VPN Detection API for Your Use Case
The right VPN detection API depends heavily on what problem you are actually trying to solve. A few frameworks for thinking about this decision clearly.
If your primary concern is analytics accuracy and geo-targeting integrity — IPinfo or MaxMind GeoIP2 offer strong geolocation accuracy combined with reliable VPN detection across the most common commercial VPN services. These are solid choices for marketing and analytics use cases where the threat model is primarily consumer VPN use rather than sophisticated fraud.
If your primary concern is fraud prevention and account security — IPQualityScore or Scamalytics offer the fraud-oriented scoring and abuse history data that security and fraud teams need. The layered risk scoring these platforms provide fits naturally into fraud decision workflows.
If residential proxy detection is a specific requirement — Spur is the most specialized option in this space and worth evaluating seriously if sophisticated actors using residential proxies are part of your threat model.
If you are already in the Cloudflare ecosystem — Cloudflare’s IP Intelligence leverages network-level visibility that no database-driven provider can match and integrates naturally with other Cloudflare security products.
If developer experience and time to integration matter most — IPinfo and Abstract API offer the cleanest documentation and most straightforward integration paths, making them strong choices when engineering time is the binding constraint.
Implementation Best Practices
Regardless of which API you choose, a few implementation principles apply universally.
Never use VPN detection as a binary block-or-pass decision without considering your false positive rate and its impact on legitimate users. Build confidence thresholds that match your risk tolerance rather than blocking everything above zero.
Cache detection results appropriately. IP characteristics do not change on every request from the same IP — caching results for a reasonable window reduces API costs and response latency without meaningfully reducing detection accuracy.
Layer VPN detection with other signals. IP intelligence is one input. Combined with device fingerprinting, behavioral analysis, and account history, it becomes significantly more powerful and significantly less prone to costly false positives.
Monitor your detection results over time. The VPN landscape changes and your implementation should be evaluated regularly against current traffic patterns rather than set up once and forgotten.
Conclusion
Masked IP traffic is not a niche technical problem anymore. It is a mainstream reality that affects analytics accuracy, advertising efficiency, fraud prevention, content licensing compliance, and pricing integrity for businesses across virtually every industry that operates online.
The VPN detection API market has matured to the point where there are genuinely excellent options available for almost every use case and budget. The gap between the best and worst providers is enormous — in data quality, detection breadth, false positive rates, and the sophistication with which they handle the hardest detection challenges like residential proxies and relay services.
The providers covered in this article represent the strongest options available in 2025 across the spectrum of use cases and sophistication levels. Choosing among them well requires clarity about your specific problem, honest assessment of your threat model, and willingness to test detection quality against your actual traffic rather than relying on vendor claims alone.
Get that right and VPN detection becomes a genuine operational asset rather than another API integration that promises more than it delivers.

Leave a Reply